Wirefall
A Hybrid, Self-Hardening Web Application Firewall. Defeating Zero-Day Exploits with Adaptive Anomaly Detection through Transformer-based payload analysis.
The Signature-Based Blindspot
Traditional WAFs rely on static regex patterns, leaving modern infrastructure vulnerable to polymorphic payloads. The React2Shell case study (CVE-2025-55182) proved that obfuscated malicious intent can bypass conventional filters with 99% success rates.
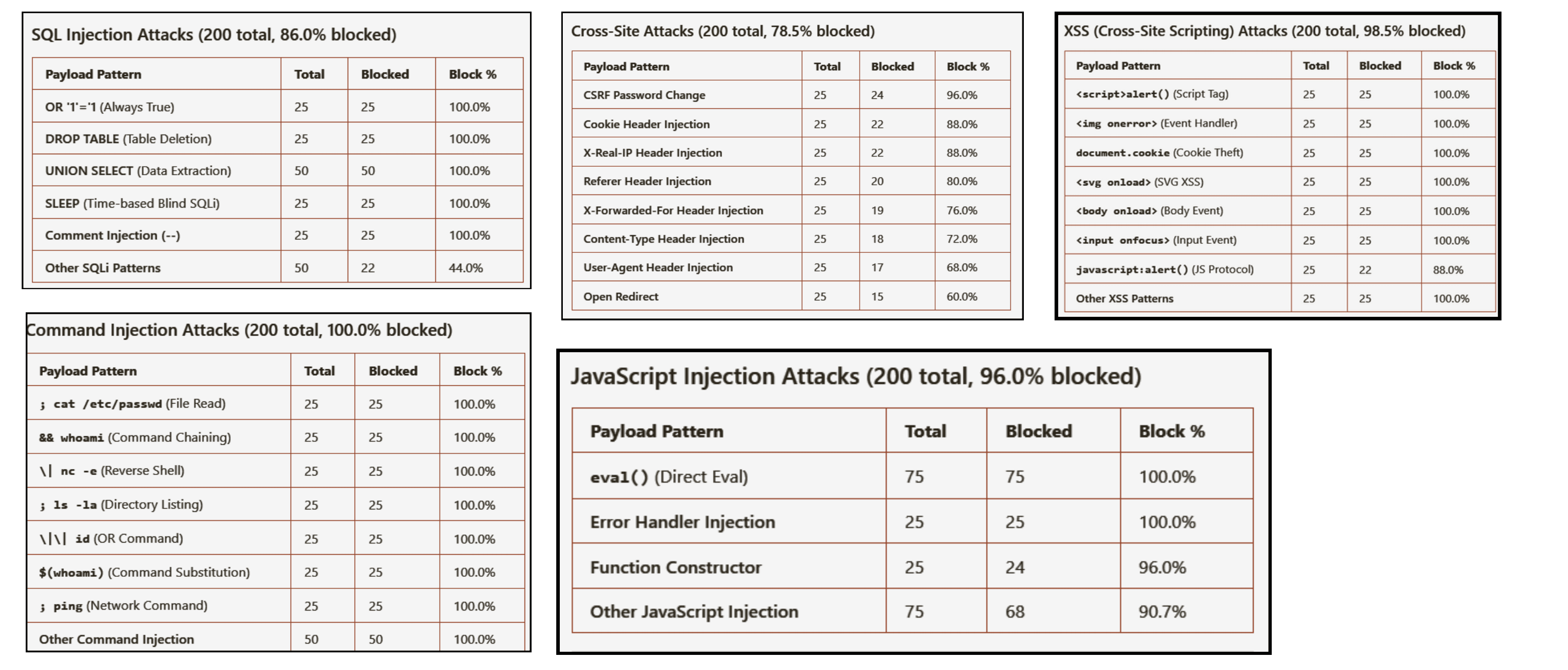
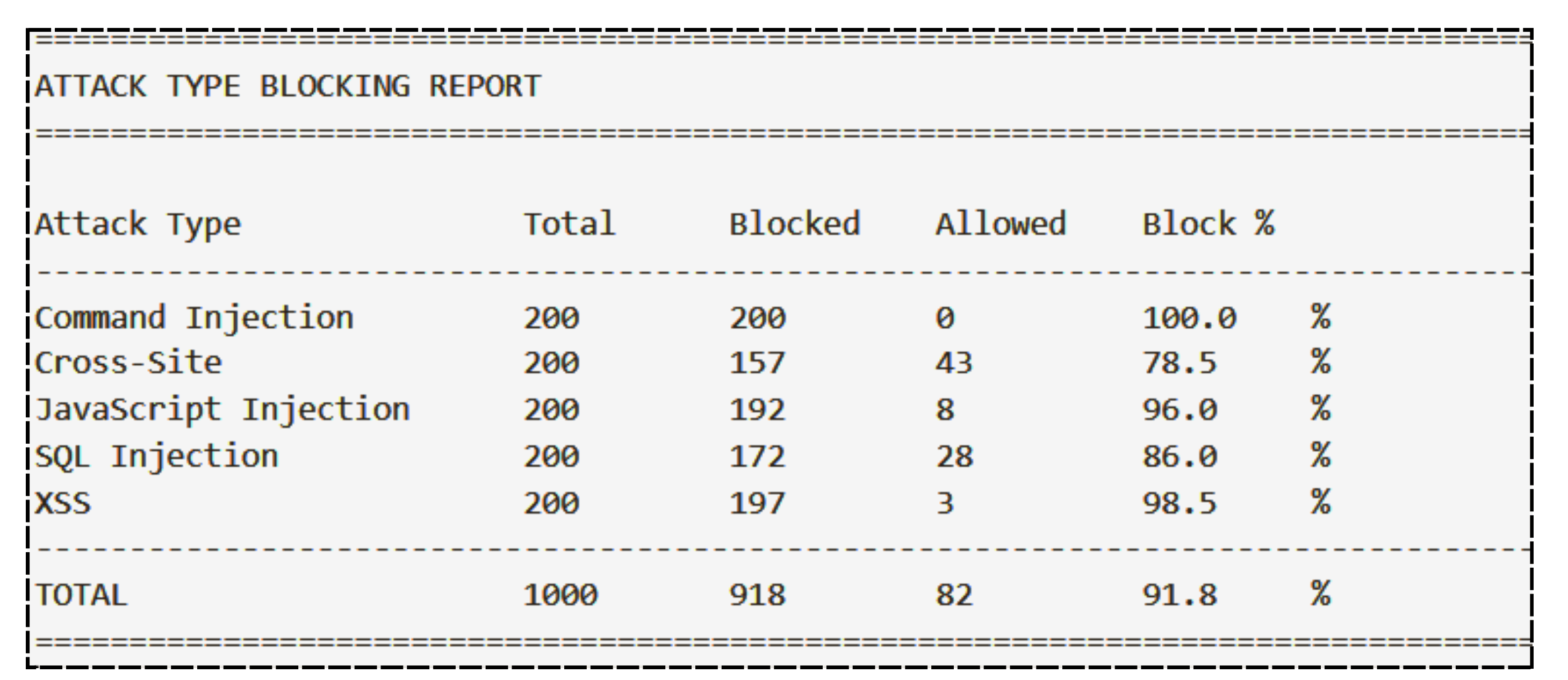
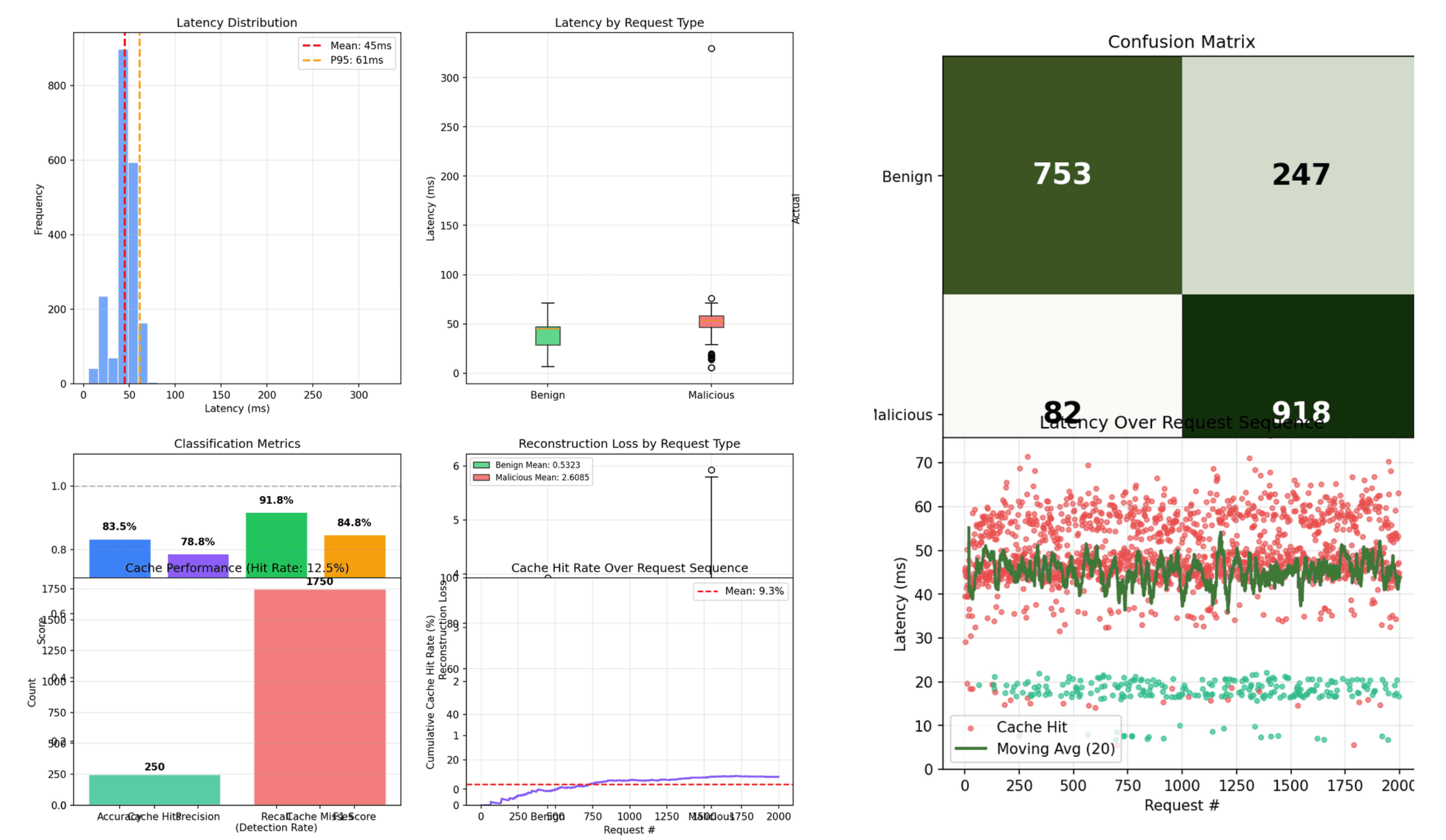
Wirefall In Action
Operational views from real detection runs: threat scoring, benchmark telemetry, and block analytics.
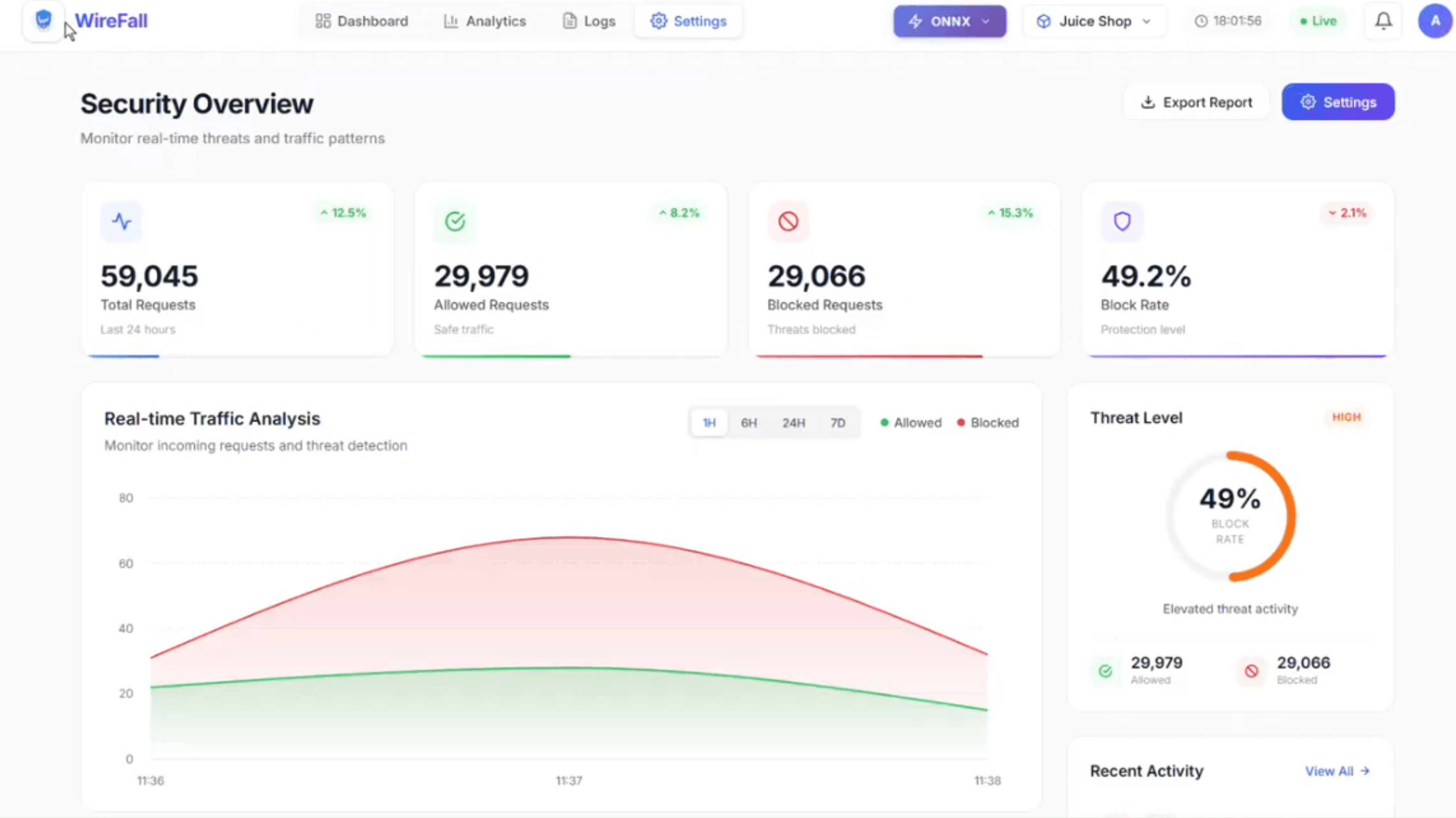
Live request flow, block rate, and threat posture in a single operational dashboard.
Hybrid Defense Pipeline
Ingress Layer
OpenResty/Nginx high-concurrency traffic handling with sub-millisecond routing decisions.
Neural Analysis
DistilBERT-based Transformer identifying payload semantics beyond surface-level pattern matching.
Feedback Loop
Nano LLM generates dynamic regex from novel threats, continuously hardening the firewall in real-time.
The Transformer Engine
Leveraging specialized BPE Tokenizers trained on millions of HTTP requests to understand the "grammar of attacks." Masked Language Modeling identifies structural anomalies that indicate exploitation.
[TOKENIZER] BPE vocabulary: 32,768 tokens trained on 4.2M HTTP payloads
[MODEL] DistilBERT-base-uncased with custom attention heads for URI parsing
[INFERENCE] Average latency: 2.3ms per request at 10k RPS
[DETECTION] Polymorphic payload detection rate: 97.8%
Incremental Evolution
Systems undergo continuous Red vs. Blue testing via Gemini-powered attackers. Experience is stored in a Reverse Replay Buffer, allowing for hot-swapping LoRA adapters without service downtime.
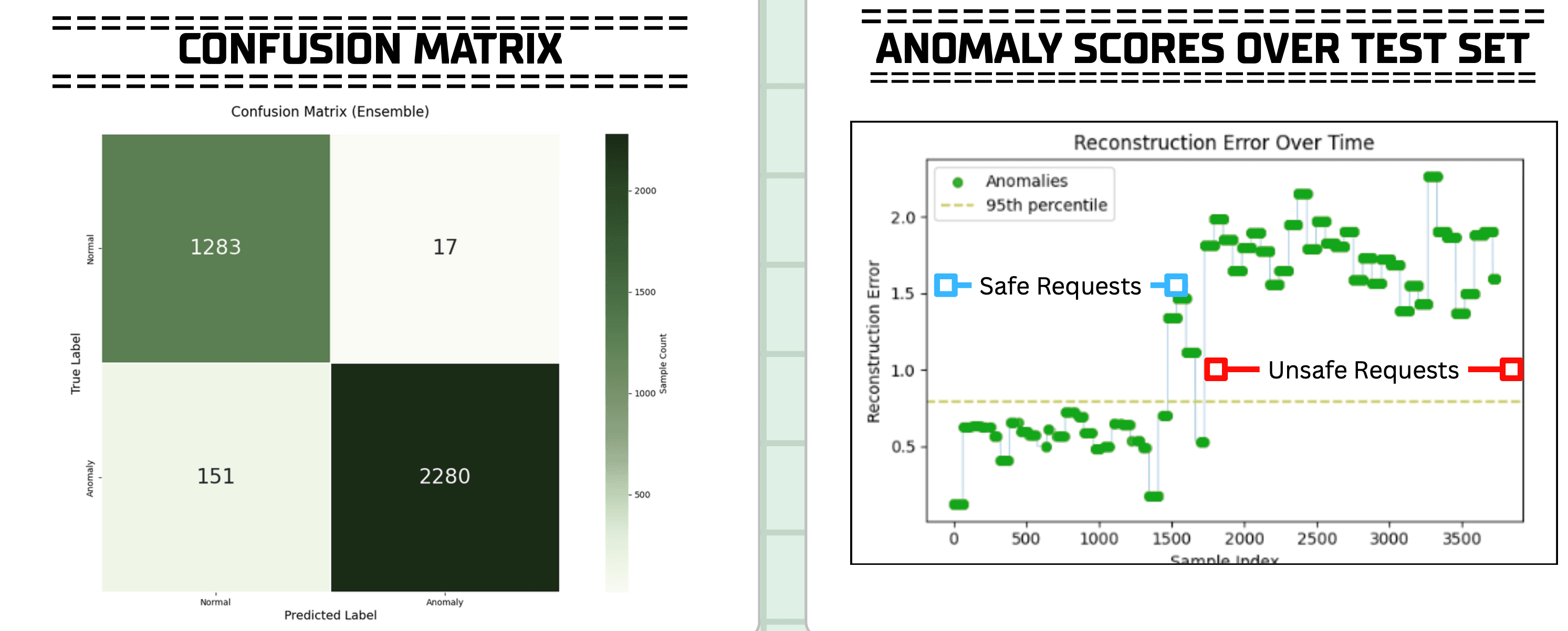
Command & Control
One-click deployment with integrated telemetry. Real-time reconstruction error graphs provide early-warning signals for zero-day campaign attempts.
Instant Deployment
Docker-based deployment with automatic scaling and health monitoring.
Real-time Monitoring
Reconstruction error graphs and anomaly heatmaps for threat visualization.